Origin Story
From breaking game state variables to dissecting network packets, my curiosity has always lied in understanding how systems work under the hood, so that I can figure out how to break them.
Here is the timeline of how I got into cybersecurity and where I'm headed.
My Cybersecurity Journey:
The Spark: Infinite Cash
It all started with games. I wasn't satisfied with playing by the rules, but back then, you couldn't just download a "Mod APK" off the internet to get unlimited coins. I had to figure it out manually.
I spent hours digging into game configuration files and memory states, manually modifying HEX values just so I could max out my in-game cash. I didn't know it at the time, but cracking those simple games taught me the core fundamentals of memory allocation and reverse engineering.
The Android Modder
My curiosity quickly scaled from games to operating systems. I became obsessed with Android internals: unlocking strict bootloaders, ripping out carrier bloatware, creating custom boot animations, and flashing custom ROMs natively.
But I wanted more control. I started pushing Android emulation to its absolute limits on PC—migrating from rigid emulators like Bluestacks and Nox to fully installing embedded Android operating systems like Prime OS, Phoenix OS, and Abstergo OS onto bare metal.
It was through this obsessive tinkering with kernels and partitions that I stumbled upon the architecture that would change everything: Linux.
Going Offensive: Kali & CVEs
College was the turning point where "tinkering" evolved into actual offensive security. I installed Kali Linux and never looked back.
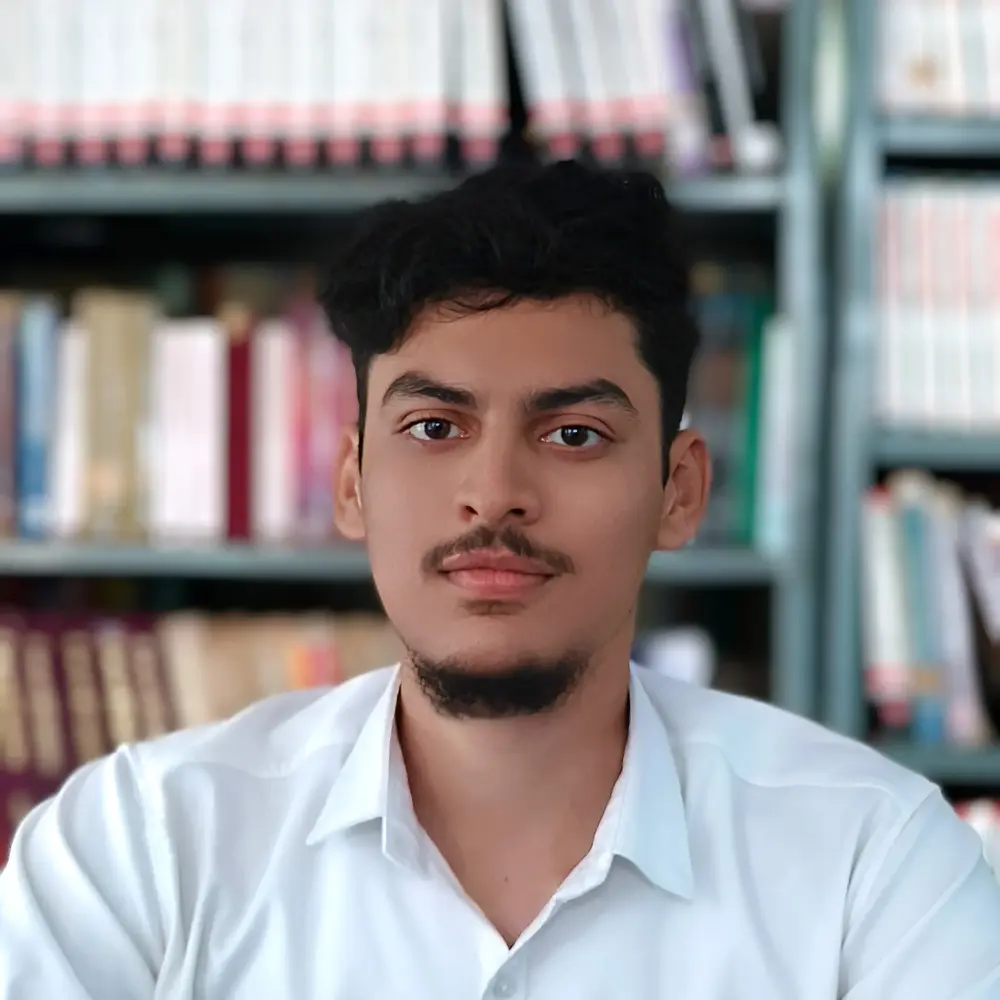
I built complex homelabs, clustered target VMs, and relentlessly pursued certifications like my CEH Master to validate my skills. My mindset shifted from just breaking things to deeply understanding how enterprise architectures fail.
This culminated in a pivotal moment: tearing apart an educational ERP system used by over 100 institutions across India, finding a massive blind spot, and officially coordinating the disclosure of a critical severity CVSS 9.8 Remote Code Execution flaw (CVE-2025-14598).
Deciphering Cybersecurity: SifrSec
Today, I'm absolutely committed to making cybersecurity my lifelong career. But the industry is clouded with too much noise and too few real practitioners.
That's why I'm launching my own media platform and community: SifrSec.
Through the SifrSec YouTube channel and sifrsec.dev platform, my mission is to tear down the gatekeeping in technical security education. I'm focused on delivering raw, practitioner-first content spanning vulnerability research, hardware hacking, and red/blue team defensive architecture. No fluff.




Let's connect
Get in touch
Have an interesting project or want to collaborate on security research? My inbox is always open.
Reach out to discuss offensive security roles, SifrSec, or just to talk cybersecurity.